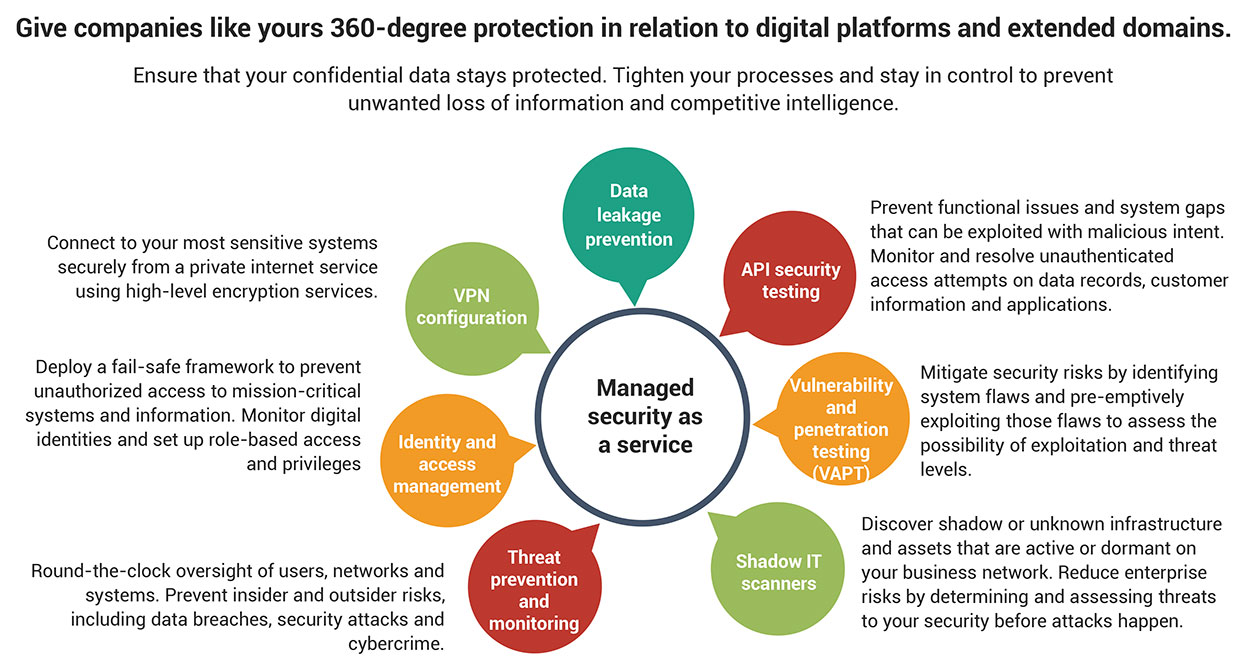
How secure is your business data?
Fact: Security attacks are increasing in scale and sophistication.
Fact: Enterprise on-premise software is no longer a viable defense solution against threats and vulnerabilities in cyberspace.
Fact: Your IT teams are investing a tremendous amount of time and effort just to stay on the defensive – this is valuable time that is better spent on strategic revenue-generating activities.
No matter how big your IT infrastructure, chances are, unless you are in the business of cyber security, it takes a lot of dedication to keep up with the exponential technological growth and complexity of cyber warfare. Your security roadmap is better-managed in the hands of a specialized service provider, who is well-equipped to give you the required proactive protection, expertise and infrastructural support to monitor, mitigate and resolve security threats.